Key Points:
- No matter your business size, you are susceptible to business or workplace fraud.
- Workplace fraud can happen in any industry, so it is important to make sure that you take all necessary precautions.
- Making your employees aware of the common types of fraud may save your business from attacks.
Think your business is immune to fraud? Think again. Every company needs a business fraud protection plan in place.
Every business is susceptible to fraud, no matter the size or type of business. Business fraud is not just for small businesses. According to Peoria magazine, mid-sized companies with less than 100 employees can lose $190,000 on average from business fraud attacks.
Business fraud is a broad term that encompasses many types of crime against your organization. Whether stealing funds or sensitive data, business fraud is a severe threat. In this post, we’ve developed ten tips to help you prevent fraud.
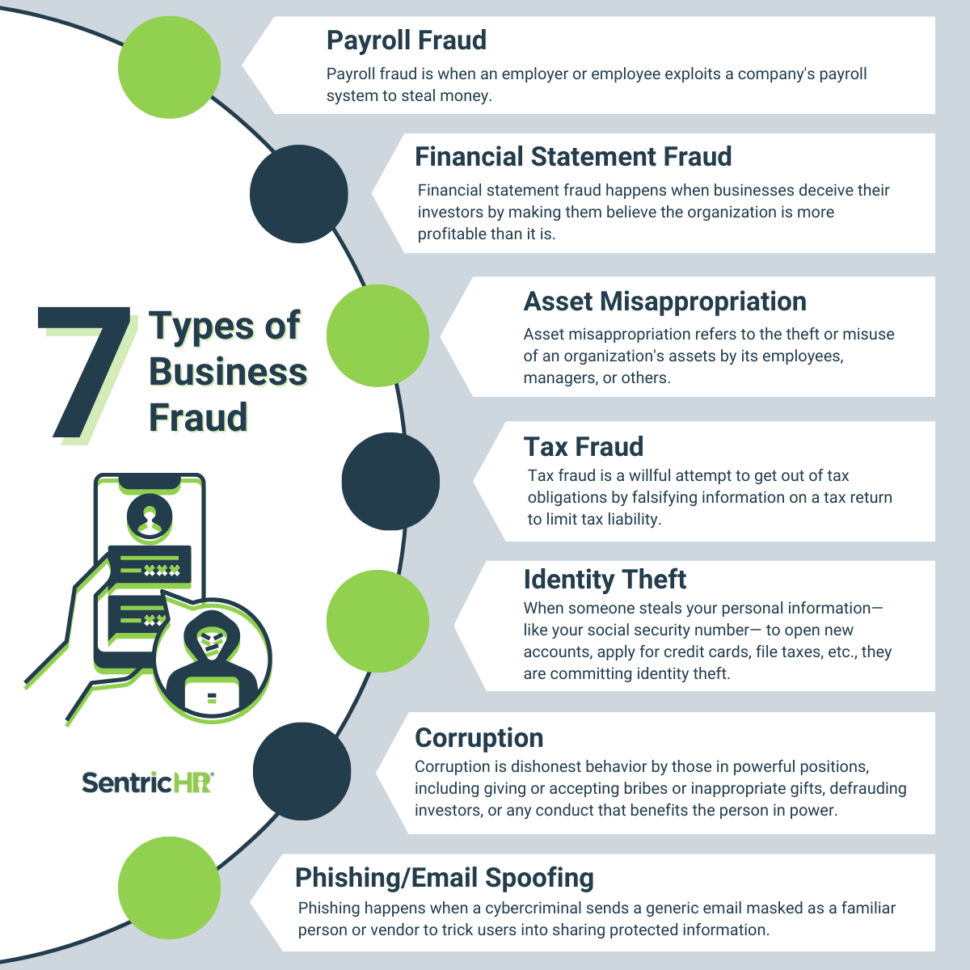
7 Types of Business Fraud
Workplace fraud happens in a number of different ways. In order to keep your company protected, you need to know about the most common forms of business fraud. Let’s take a look at the 7 most common types of business fraud you need to know:
- Payroll Fraud
Payroll fraud is when an employer or employee exploits a company’s payroll system to steal money. People commit payroll fraud by submitting false timesheets to earn someone more pay than they deserve, issuing unauthorized bonuses, or sending money to a fake employee or an ex-employee.
Here are a few signs that you can be aware of:
- Gaps or errors in payroll records
- Unfamiliar Changes in payroll records
- Employees who list identical addresses, social security numbers, or bank account details
- Unexpected emails concerning payroll
- Financial Statement Fraud
Financial statement fraud happens when businesses deceive their investors by making them believe the organization is more profitable than it is. According to Investopedia, this type of business fraud is one of the least common, only accounting for about 10% of cases of fraud. Although it doesn’t happen as often as other types of business fraud, financial statement fraud is one of the most costly types of workplace crime.
Signs of financial statement fraud include:
- Accounting abnormalities like unexplainable growing revenues
- A significant surge in your company’s performance within the final reporting period
- Rising income without corresponding cash flow
- Consistent sales growth while competitors are struggling
- Asset Misappropriation
Asset misappropriation refers to the theft or misuse of an organization’s assets by its employees, managers, or others. Misappropriation of assets includes theft of cash, sensitive data, or office equipment.s It also includes fraudulent financial transactions, such as embezzlement, check tampering, or billing schemes.
The following are a few common signs that your business is a victim of asset misappropriation:
- Unexplained budget overruns
- Unexplained changes in accounting records
- Inventory shortages
- Altered check amounts
- Unusually large or numerous credits are applied to a particular account
- Duplicate payments
- Tax Fraud
Tax fraud is a willful attempt to get out of tax obligations by falsifying information on a tax return to limit tax liability. Examples of tax fraud include:
- Claiming false deductions.
- Claiming personal expenses as business expenses.
- Using an incorrect social security number.
- Need to record income.
Another common form of tax fraud is tax evasion, which refers to illegally avoiding payment of taxes owed.
The following are common red flags to look for as an indication of tax fraud:
- Claiming an inaccurate number of dependents
- Claiming residency in another state
- Closing and starting new businesses repeatedly
- Concealing financial or personal assets
- Missing records
- Having weak financial controls
- Identity Theft
When someone steals your personal information— like your social security number— to open new accounts, apply for credit cards, file taxes, receive medical services, or even use your name to present to law enforcement, they are committing identity theft. This type of fraud will negatively affect your credit and put you at risk of being sued for not paying debts or being arrested.
The following are signs that you are a victim of identity fraud:
- Receive credit cards that you didn’t apply for
- Find unauthorized charges and fraudulent transactions on your bank or credit card statements
- Receive bills or collection letters from companies or accounts you don’t recognize
- Receive rejection letters from jobs you never applied for
- Get calls from debt collectors
- Corruption
In general terms, corruption is dishonest behavior by those in powerful positions. Corruption includes giving or accepting bribes or inappropriate gifts, defrauding investors, or any conduct that benefits the person in power. When you report corruption, expect your business to experience unflattering media attention, dampened growth and development, or stunted investments.
The following are common red flags or signs of corruption in the workplace:
- Inappropriate purchases
- Questionable invoices
- Conflicts of interest
- Incomplete travel and expenses
- Phishing/Email Spoofing
Phishing happens when a cybercriminal sends a generic email masked as a familiar person or vendor to trick users into sharing protected information. Spear phishing is another type of cyber attack This type of phishing explicitly targets users with a very believable message, meaning they’ve researched you and your company. They also focus on finding ways to get a user to open malicious Word or PDF documents.
Along the same lines as spear phishing, email spoofing has become popular among cybercriminals. Proofpoint defines email spoofing as a technique used in spam and phishing attacks to trick users into thinking a message came from someone they know and can trust.
If you come across an email that you suspect may be fraudulent, ask yourself the following questions:
- Does the “From” address match the display name in the email?
- Does the “Reply-to” match the source of the email?
- Is the email asking you to authenticate or update your information in an urgent tone?
In any case, if you are unsure of an email you receive or the content is asking you to click a link to authenticate or update your information, always check with your IT team.
10 Business Fraud Protection Tips
Unfortunately, you may not know you are a victim of fraud until after it happens. Still, there are multiple ways you can prevent it from happening. The following are ten of the most helpful fraud provention strategies you can implement to protect your organization:
- Two-factor authentication for all logins
Employers rely heavily on HR processes for recruiting to offboarding. These processes have greatly improved with online platforms
Two-factor authentication is a security measure that requires users to provide two forms of identification to access an account or system. It involves a combination of something the user knows, such as a password, and something the user has, such as a code sent to their phone or a physical token. Requiring two authentication factors makes it more difficult for unauthorized users to access an account.
- Change passwords regularly
McAfee says employees should be encouraged to change their computer, email, and other account passwords every 90 days. When you change your password, it makes it harder for hackers to gain access to your accounts and sensitive data. If a hacker obtains your password, changing it means they only have access for a limited time. Additionally, changing your password on a regular basis helps protect against password reuse attacks. A password reuse attack is when a hacker tries to use the same password across multiple accounts.
- Never store credit card numbers or other sensitive data on your computer
Storing sensitive data like credit card numbers, passwords, or social security numbers will put your business at risk for multiple types of fraud. The more information you store on your computer or network, the more information that is open for hackers to steal.
- Limit access to sensitive data
Every employee has a certain amount of data they can access depending on their job role. Employees who don’t need access to specific information should not have access to that information. Limiting access is a common way to protect your organization’s data. For example, your marketing team should not need access to any customer’s payment information.
- Require your employees to use a VPN
A Virtual Private Network (VPN) is a protected network connection you can use when using public internet connection. VPNs encrypt your internet traffic and disguise your online identity. When your online identity is protected, it is more difficult for third parties to track your activity or access your data. Using a VPN will:
- Encrypt your IP address
- Encrypt protocols
- Kill switch
- Two-factor authentication
- Ensure your hosting provider has safeguards in place
Hosting providers offer a wide range of web hosting services including data storage, related software, servers and hardware, IT support, and cybersecurity. When choosing a hosting provider for your website, you may focus primarily on features and price. However, it is important to look for a hosting provider that safeguards and protects your website. Choosing the right provider will save your business from many fraud attempts. Look for the following security features in a hosting provider:
- Backups
- Network Monitoring
- Firewalls
- Malware Scanning
- Internal Security
- Spam filtering
- Know your employees
Just as you need to protect against outside threats, there is also a need to protect against threats inside your organization. You trust your employees with sensitive data daily, which puts your company at significant risk if you don’t hold those employees accountable.
Internal fraud causes financial statement fraud, tax fraud, corruption, data theft, or reputational damage. Always require background checks before hiring new employees and limit access to the information your employees can view.
- Perfect your internal procedures
When dealing with security processes, making and receiving payments, or signing sensitive documents, every company should follow a rigid procedure. Make sure your staff is aware of these procedures and communicate any consequences that be a result of not following internal processes correctly.
- Insure your business
Business insurance covers the costs of property damage and liability claims, and it can save you from paying out-of-pocket for any damages or legal claims. In addition to protecting you from the aftermath of a cyber attack, business insurance can cover you from property damage, libel, slander, workers’ compensation, and lawsuits. Business insurance is helpful for any organization, as about 60% of small businesses go bankrupt within six months of a data breach or a cyber attack. Not only can business insurance policy save your business from bankruptcy due to cyber attacks, but it protects your employees, customers, and management. Getting business insurance also builds credibility for your organization.
- Educate employees
Training your employees to detect common types of fraudulent activity is one of the best ways to avoid a significant security breach. Building a fraud training program for your workplace begins with understanding all kinds of fraud and the risks they bring to your company. Provide example cases, “what-if” scenarios, and knowledge checks to ensure employees fully understand the types and dangers of business fraud.
The bad news is that no matter what, cybercriminals will try to execute their plans on your business. The good news? You can take steps to protect your business and employees. Learn more about business fraud prevention and how SentricHR can help with ongoing reporting, monitoring, and more.